No products in the cart.
Sale!
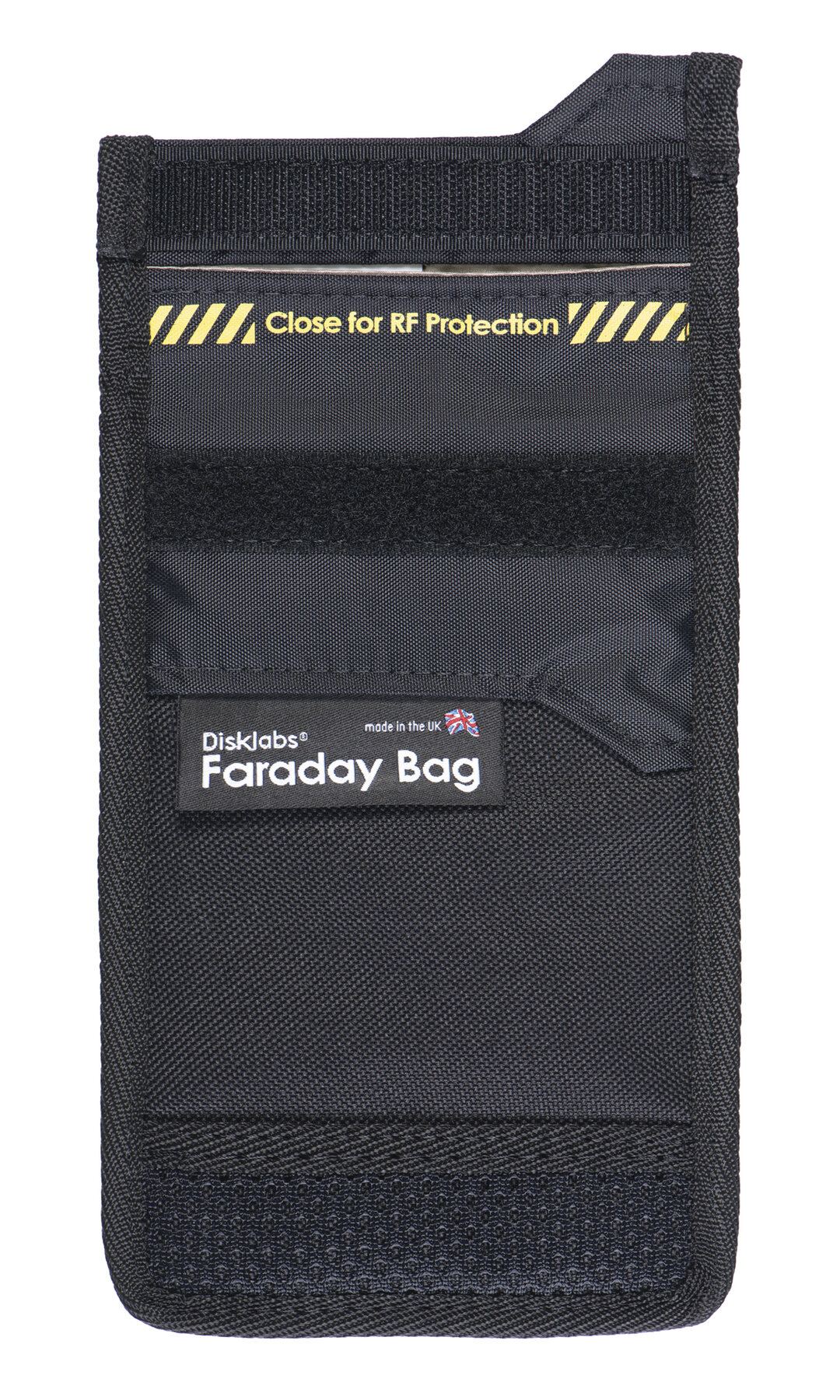
Disklabs Phone Shield Faraday Bag (PS1)
RM329.00 RM269.00
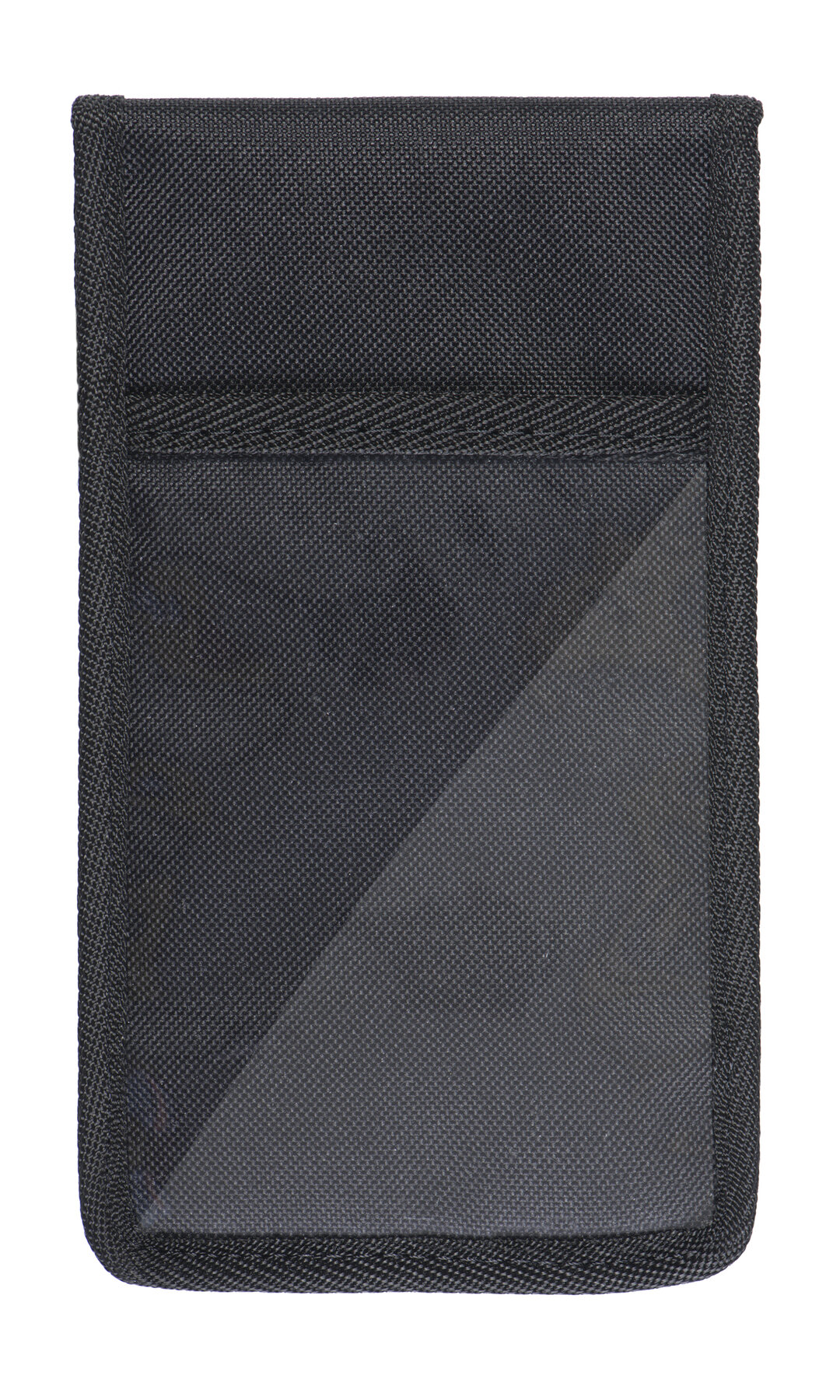
A small, windowless bag that will isolate one mobile phone, GPS or other similar-sized device. It is used to ensure that mobile phones cannot be connected to remotely, preventing remote hacking, remote wiping of data/evidence and remote surveillance.
- ✅ SECURITY – The Disklabs PS1 Phone Shield was designed for securing a smart phone from any outside interference. Perfect for securing your device from unwanted interference including remote wipe, remote location tracking, preserving evidence etc.
- ✅ ACCREDITED – This Disklabs PS1 Phone shield Faraday Bag has been awarded the Police Approved “Secured by Design” award, and is the only smarphone Faraday bag in the UK to gain Police Approval.
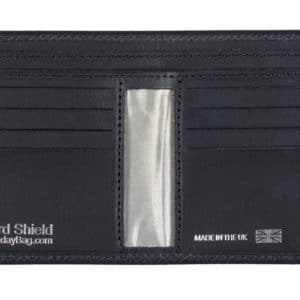
- ✅ PIECE OF MIND – Once your smart phone is sealed inside this PS1 Phone Shield Faraday bag, the Faraday lining will ensure that ALL radio signals attempting to reach your device are shielded and blocked completely.
- ✅ MADE IN BRITAIN – All Disklabs Faraday Bags are made in Britain from high quality materials to ensure they block All Wireless Signals including WiFi, 5G, 4G, 3G, 2G, GSM, GPS, Bluetooth, Radio, NFC etc.
- ✅ DESIGN – The Disklabs PS1 Phone Shield is designed specifically for protecting your smartphone upto the size of an iPhone XS Max (approx 160mm x 80mm). It can also be used to protect 2 sets of keyless entry car fobs from relay crime.




















Reviews
There are no reviews yet.